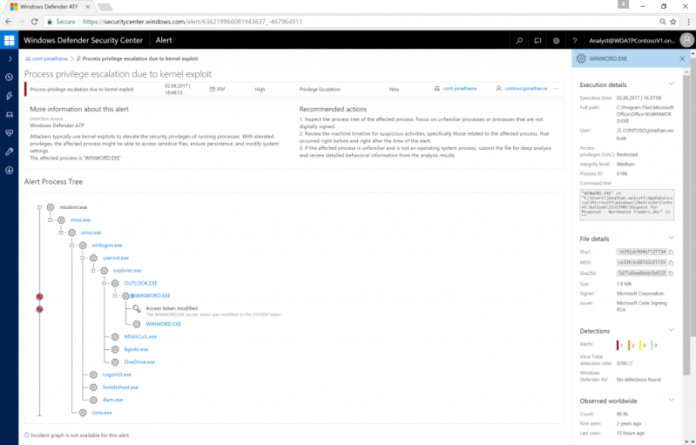
Microsoft today pushed out a fix for their virus scanning engine in Windows Defender, the MsMpEng malware protection engine. The vulnerability was discovered by Google’s Project Zero researcher Tavis Ormandy which was privately disclosed to Microsoft.
This new vulnerability would allow applications executed in MsMpEng’s emulator to control the emulator by including the remote code execution when Windows Defender scanned an executable sent by email.
MsMpEng which includes a full system x86 emulator to execute untrusted files runs an NT AUTHORITY\SYSTEM and which is not sandboxed. Microsoft had given the emulator an extra instruction to allow API calls which is a potentially bad vulnerability.
To explain Ormandy Wrote:
“Command 0x0C allows you to parse arbitrary-attacker controlled RegularExpressions to Microsoft GRETA (a library abandoned since the early 2000s)… Command 0x12 allows additional “microcode” that can replace opcodes… Various commands allow you to change execution parameters, set and read scan attributes and UFS metadata. This seems like a privacy leak at least, as an attacker can query the research attributes you set and then retrieve it via scan result”.
The vulnerability was found on 12th May by the Google’s Project Zero team and the Redmond Giant pushed out a fix last week which now has fixed the Vulnerability and now most user should no longer be vulnerable.