You’re not alone if you’re getting a “Kernel-mode Hardware-enforced Stack Protection is off. Your device may be vulnerable” warning when you open Windows Security in Windows 11 version 22H2 or 22H1.
After the latest Windows Defender update, Windows 11 users report that Windows Security shows a new “Kernel-mode Hardware-enforced Stack Protection is off. Your device may be vulnerable” warning. The warning doesn’t go away when users try to enable the feature, likely due to issues with drivers.
For those unaware, a recent bug in Windows 11 erroneously warned users that Local Security Authority (LSA) Protection had been disabled, even though it was toggled on. As LSA protection is a crucial security feature that defends against login credential theft, this widespread false error caused concern among users.
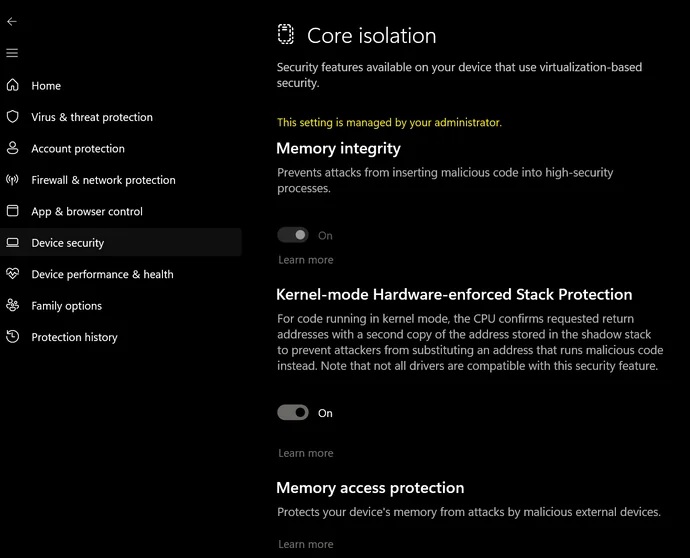
Today’s Microsoft Defender update has resolved the LSA problem. This update replaces the Local Security Authority (LSA) Protection settings in Windows Security with Hardware-Enforced Stack Protection. With the LSA warning now resolved, the update has introduced a new warning related to Hardware-Enforced Stack Protection.
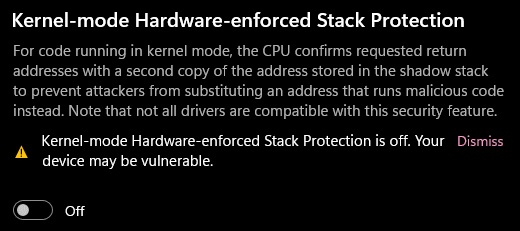
However, unlike the previous LSA warning, this new warning does not appear to be a false positive. The disabled Hardware-Enforced Stack Protection seems to result from incompatible drivers or apps, such as anti-cheat systems.
This change is rolling out as part of a mandatory security update and is installed automatically.
If you’re running into “Kernel-mode Hardware-enforced Stack Protection is off. Your device may be vulnerable” warnings, a driver or app is likely preventing the feature from working.
We have received several emails and comments from users confirming the mess. Users have reported that their kernel-mode hardware-enforced Stack Protection is disabled by default, and attempts to enable it have been unsuccessful.
The problem appears to stem from driver compatibility issues, although the specific driver causing the conflict remains unclear.
Some have linked the issue to Bitlocker, as Microsoft Defender Antivirus updates (KB5007651 and KB2267602) seem to have introduced a conflict with Bitlocker Countermeasures.
Bitlocker Countermeasures, including Pre-boot authentication, enable the Group Policy “Require additional authentication at startup,” which is active on some systems. According to the Kernel DMA Protection support document, this feature is incompatible with other BitLocker DMA attack countermeasures.
When users receive a message stating that hardware-enforced Stack Protection cannot be turned on due to driver incompatibilities, clicking “Review Incompatible Drivers” yields no results.
What is causing kernel-mode hardware-enforced stack protection is off warnings?
The short answer is the Windows Security app is not good at detecting the incompatible driver, and it may be impossible for users to troubleshoot the problem.
For those unaware, “Hardware-enforced Stack Protection” is a new Windows 11 feature which enables apps or games to leverage local CPU hardware to safeguard their code. It aims to protect the memory stack, which is the place where app codes are stored during the execution of the program.
The security feature can protect the code by managing the memory stack through modern CPU hardware and shadow stacks (code’s execution order). It is a hardware-based security feature in newer processors, and it won’t work with certain apps or drivers, such as outdated anti-cheat systems or keyboard/mouse drivers.
For example, you won’t be able to enable the feature if you have Riot Vanguard (vgk.sys), GameGuard or similar apps. To enable the feature, you’ll need to uninstall them.
Windows Latest understands that Microsoft is exploring a better way to detect and flag incompatible drivers so that users can make changes.
It is worth noting the warning in Windows Security app may suggest your device is “vulnerable” but doesn’t necessarily mean your device is under attack. Hopefully, Microsoft will improve the Windows Security app’s warnings sooner rather than later for everyone.